The latest entry in the Beer Tray series- This is a Christian Feigenspan tray. Great artwork on this tray, promoting thre Feigenspan Brewing Company of Newark, New Jersey. The brewery used the PON initials (Pride Of Newark) as part of its logo.

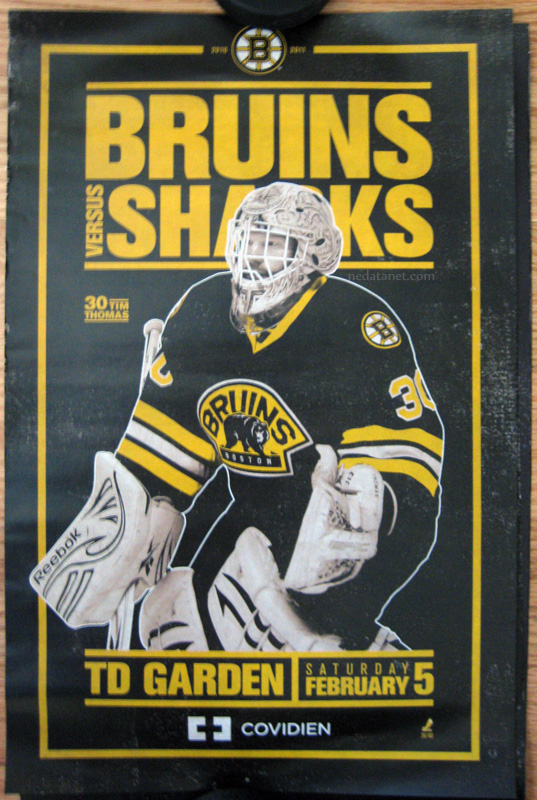
Boston Bruins Gameday Posters- Bruins vs Sharks
Boston Bruins vs San Jose Sharks gameday poster – featuring Tim Thomas
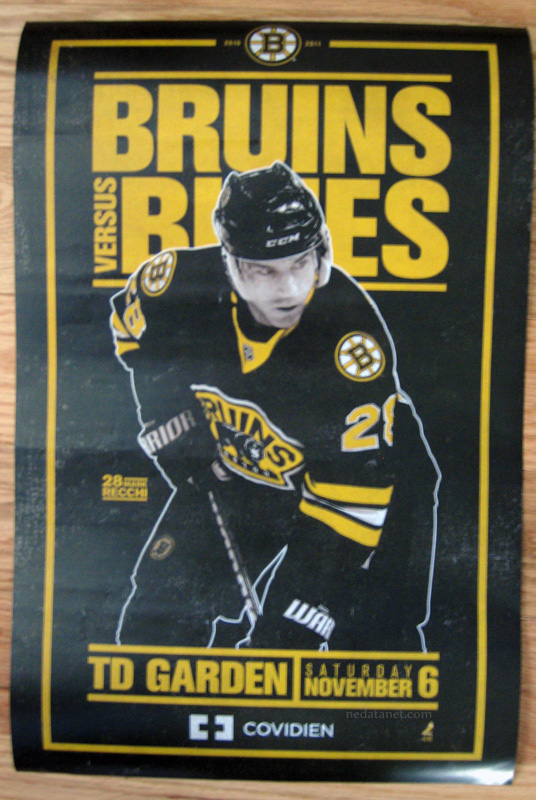
Boston Bruins GameDay Posters – Bruins v Blues
Boston Bruins gameday poster – Boston Bruins vs St Louis Blues, featuring Marc Recchi
Mgmt Info Sec Notes Week1
1. List and describe an organization’s three communities of interest that engage in efforts to solve InfoSec problems. Give two or three examples of who might be in each community.
The three defined communities are decision makers in Information security, Information technology and non-technical staff. Examples of Information security professionals could include a risk manager or the CISO. The information technology group could include the CIO or a systems administrator. Some examples of Non-technical members could be the CEO or the Director of Human Resources.
2. What is the definition of Information Security? What essential protections must be in place to protect information systems from danger?
From the lecture material: “The protection of information and its critical elements (confidentiality, integrity and availability), including the systems and hardware that use, store, and transmit that information” Essential protections that must be in place include physical security, operations security, communications security and network security.
3. What is the C.I.A. triangle? Define each of its component parts.
- Confidentiality -only those who are granted access can get in
- Integrity- data is true and uncorrupted
- Availability – if granted access, data is available without obstruction
4. Describe the CNSS security model. What are its three dimensions?
• The McCumber Cube is a comprehensive information security model that covers the three dimensions of information security – the CIA triangle, data states (storage, processing and transmission) and controls (policy education and technology).
5. What is the definition of privacy as it relates to information security? How is this definition of privacy different from the everyday definition? Why is this difference significant?
The text describes privacy as “Information that is collected, used and stored by an organization is intended only for the purposes stated by the data owner at the time it was collected” and a dictionary describes it as “the state of being free from intrusion or disturbance in one’s private life or affairs”. The expectation of privacy does not extend into the Information Security model; it does not guarantee freedom from observation, only that any data gathered will be used in an expected and declared manner.
6. Define the InfoSec processes of identification, authentication, authorization and accountability.
- Identification –An individual user or process is named and unique
- Authentication – A control verifies that he user is who they say they are, usually possessing something they have (example a certificate) or something they know (example: a password)
- Authorization – Explicit permission to an identifiable and authenticated user has been granted to access a resource.
- Accountability- A user or processes’ actions can be logged or otherwise tied back to the originating account.
7. What is management and what is a manager? What roles do manager play as they execute their responsibilities?
From the lecture notes: Management is “The process of achieving objectives using a given set of resources “A manager is “Someone who works with and through other people by coordinating their work activities in order to accomplish organizational goals“. Managers use different roles to accomplish objectives. In an informational role, managers collect process and use information. In an interpersonal role, managers work with people to achieve goals. In a decisional role, managers make choices as to the best path to take and address issues that arise while using problem solving skills.
8. How are leadership and management similar? How are they different?
Good leadership and management are intertwined. Management focuses on the planning and strategic decisions, and leadership provides the motivation to implement the planning and organizing functions.
9. What are the characteristics of management based on the popular approach to management? Define each characteristic.
The popular approach to management includes
- Planning- Goals, objectives, strategizing and plans
- Organizing- Structure, Human resource allocation
- Leading- Motivation, leading, communication, group dynamics
- Controlling- Standards, measurement, comparisons, action
10. What are the three types of general planning? Define each.
- Strategic Planning- Long term goals, 5 or more years
- Tactical Planning- Production planning, one to five years, smaller scope then enterprise planning
- Operational Planning – Day to day operations, short term goals.
Budweiser Beer Tray
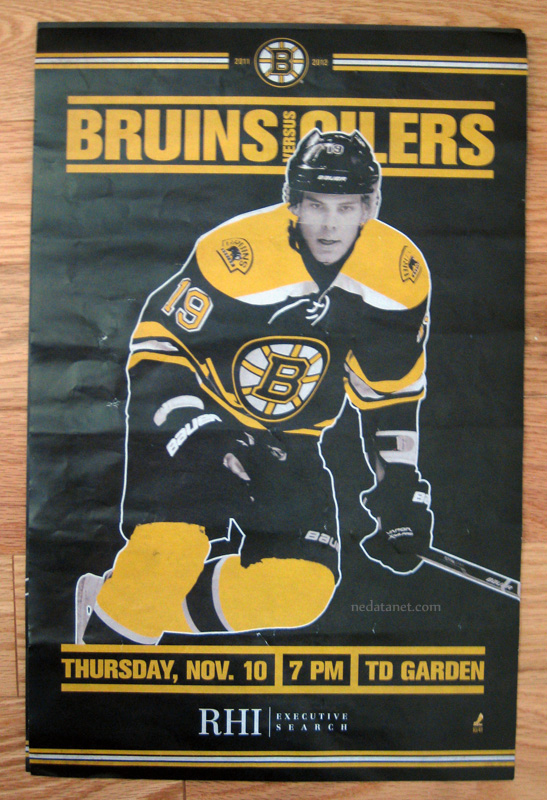
Boston Bruins GameDay Posters – Bruins vs Oilers
For the past 3 seasons, the Boston Bruins have been handing out a small poster sized gameday roster. The front features (typically) a player, and the back has rosters for both teams, and other information about the featured player, game notes, the upcoming schedule, etc. These posters look similar to the old fight posters promoting boxing matches. This is today’s example: Boston Bruins vs the Edmonton Oilers, featuring Tyler Seguin on the front. As a note, its notoriously hard to get one these home without too many wrinkles, tears, folds and such.
Bavarian Porter Beer Tray
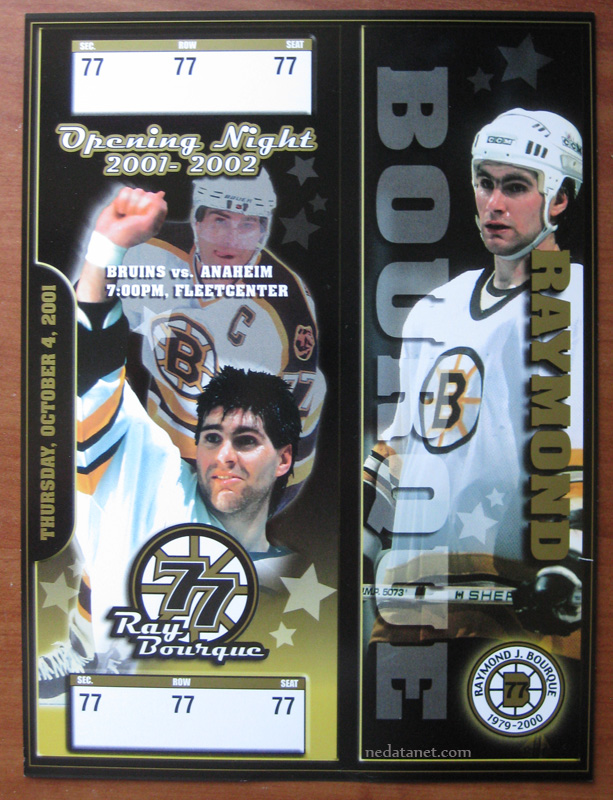
Ray Bourque Retirement Night Commemorative Ticket
This is an image of a promotional giveaway ticket from the night Ray Bourque’s number was raised to the rafters in Boston. The Bruins honored Bourque, one of the Bruins most beloved hockey players, on October 4 2001 in front of a packed house before the Bruins played the Anaheim Ducks that evening.
Mgmt Info Sec Chap 5 Notes
1. What is an information security program?
- An information security program describes the structure and organization of the effort that strives to contain the risks to the information assets of a company.
2. What functions constitute a complete information security program?
- A complete information security program is unique to the company, and takes into account business goals and the overall strategic plan, but still balances the need for protecting the assets of the organization.
3. What organizational variables can influence the size and composition of an information security program’s staff?
- Organizational culture- the value placed on security by managerial staff can define the resources committed to security staff.
- Size- the size of the company influences the size of the security staff.
- Security personnel budget – Funds allocated to the program
- Security capital budget – Items in the capital budget can determine staffing needs.
4. What is the typical size of a security staff in a small organization? A medium sized organization? A large organization? A very large organization?
- Small – May be delegated to an IT staffer or manager
- Medium – 1 full time manager and assistance from IT staff
- Large – approximately 17-22 employees is suggested by the text
- Very Large – 49-65 members is suggested by the reading.
5. Where can an organization place the information security unit? Where should (and shouldn’t) it be placed?
- The text suggests many organizational locations for the InfoSec unit, and lists the pros and cons for each. Recommended locations are Information technology, administrative services, insurance and risk management , the legal department, or operations.
- Non recommended locations are security, internal auditing, help desk, accounting and finance, human resources, facilities management.
- The key to any successful placement will be the reporting chain of command and resource allocation.
6. Into what four areas should the information security
functions be divided?
- Functions performed outside of IT management and control, such as legal or training
- Functions performed by IT outside of InfoSec – example: network security administration.
- Functions performed by the infoSec department such as risk assessment or vulnerability assessment
- Functions performed by the InfoSec department as compliance enforcement- examples include policy creation, compliance audits
7. What are the five roles that an information security professional can assume?
- Chief Security Officer
- Security Manager
- Security Administrators And Analysts
- Security Technicians
- Security Staff
8. What are the three areas of the SETA program?
- Awareness, Training and Education
9. What can influence the effectiveness of a training program?
- Things that may influence the effectiveness of an information security training program include management support, training that is targeted to its audience, retention of information, information overload, and the style of information delivery.
10. What are some of the various ways to implement an awareness program?
- One way to implement security awareness if to use an array of items including training videos, posters, newsletters brochures, trinkets and computer based training. By varying method of delivery, the message does not become commonplace and lose its effectiveness.
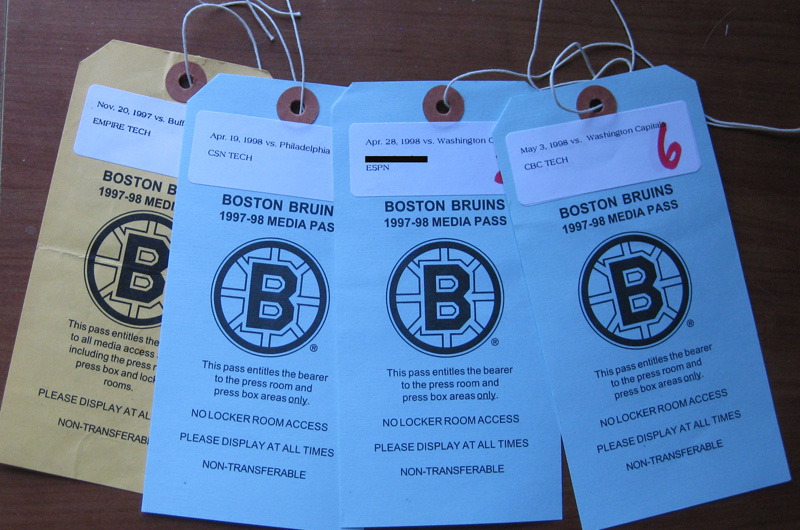
Boston Bruins Media Passes
I recently found a bunch of stuff from back in the day, including some stuff from my days as a contractor to some of the broadcast networks. Here’s a pic of some media passses from the Boston Bruins 1997 to 1998 season – the Bruins lost that year in the playoffs to the Washington Capitals.