Two examples of Ballantine’s beer trays, from the Mr.Ed collection


Author: mline
Mgmt InfoSec Notes ch 3
1. What is an information security framework?
A framework is an outline of security controls that is part of creating or implementing a security model. The blueprint is based off of the framework, containing more detail on controls in place and controls that are needed.
3. What is a security model?
A security model is a generic blueprint that assists in creating a working security plan.
5. What is access control?
Access control enables an organization to define and regulate access to data, and is based on identification, authentication, authorization and accountability.
10. What is a data classification model? How is data classification different then clearance level?
Data classification attempts to categorize information based on the level of damage that would be done if the information is exposed. The more important the data, the higher the classification level. Clearance level is a rating scheme that attempts to categorize a user’s role in an organization and access to information is granted to groups of users in each level.
11. Which international information security standards have evolved from the BS 7799 model? What do they include?
BS7799 was published by the British Standards
Institute. From this document, the ISO/IEC 27002 was released, and then later
renamed as ISO/IEC 27002. BS 7799’s second part became ISO/IEC 27001.These
purchasable standards include recommendations for information security
management for use by those who initiate, implement or maintain organizational
security. The 2005 version includes the
Plan-Do-Check- Act cycle, also known as the Deming Quality assurance model.
13. What are the documents in the ISO/IEC 27000
series?
- Risk Assessment and treatment
- Security Policy
- Organization of Information Security
- Asset Management
- Human Resource Security
- Physical and Environmental security
- Communications and Operations
- Access Control
- Information Systems Acquisition, Development and Management
- Information Systems Incident Management
- Business Continuity Management
- Compliance
14. What is COBIT? Who is its sponsor? What does it accomplish?
COBIT stands for Control Objectives for Information and Related Technologies. It provides advice for implementation of sound controls and control objectives for Information Security. COBIT provides a framework to support information security requirements and assessment needs, and breaks this into four domains: plan and organize, acquire and implement, deliver and support, and monitor and evaluate.
15. What are the two primary advantages of NIST
security models?
- NIST documents are publicly available at no charge
- Have been around for some time and are broadly reviewed, therefore close to proven.
TCP/IP Security Notes
Patterns
IP attacks typically follow a set pattern. This pattern can be recognized, and rules created to help thwart it – this pattern is refered to as an attack signature. Signatures may be used to create IDS rules.
Reconnaissance and Discovery
Would-be attackers usually engage in a well-understood sequence of activities, called reconnaissance and discovery.
During the reconaissance phase The attacker may ping sweep or port probe the target. The purpose of this reconnaissance is to find out what is running and what may be vulnerable.
PING sweep
Can identify active hosts on an IP network
Port probe
Detect UDP- and TCP-based services running on a host
The attack
Attacker focuses on the attack itself. A more seasoned attacker may cover their tracks by attempting to modify log files, or terminating any active direct connections.
One method of is a brute force attack that overwhelms a victim.
Denial of Service Attacks
Designed to interrupt or completely disrupt operations of a network device or communications
SYN Flood attack
Uses the three-way TCP handshake process to overload a device on a network
Broadcast amplification attack
Malicious host crafts and sends ICMP Echo Requests to a broadcast address
Distributed Denial of Service Attack (DDOS)
DoS attacks are launched from numerous devices, such as acommand and control botnet.
DDoS attacks consist of four main elements
Attacker
Handler
Agent
Victim
Session Hijacking
The purpose of session hijacking is to impersonate an authenticated user in order to gain access to a system
Once a session is hijacked, the attacker can send packets to the server as the victim.
RFC 2401: The goal of IPSec are to provide the following kinds of security
- Access control
- Connectionless integrity
- Data origin authentication
- Protection against replays
- Confidentiality
- Limited traffic flow confidentiality
RFC 2196: Indicated that the following documents are components of a good security policy
- An access policy document
- An accountability policy document
- A privacy policy document
- A violations reporting policy document
- An authentication policy document
- An information technology system and network maintenance policy document
Ambassador Beer Trays
DORA – DHCP Address Discovery
The four packets used in the DHCP discovery process:
D – DHCP Discover packet
O – The DHCP Offer Packet
R – The DHCP Request Packet
A – The DHCP Acknowledgement Packet
This sequence is easily remembered as DORA.
Becks Beer Tray
From Mr. Ed’s collection
Startech USB2DVIE2 USB display adapter
Adding an additional monitor with Startech USB2DVIE2 USB display adapter
Adding an additional display to an older machine can be expensive and complex. ATI’s multi monitor eyefinity solution requires a new card to be purchased and installed, which is simple enough if a card is available for the specific AGP, PCI or older spec PCIE slot on the motherboard. The cost can scale from 100.00 and up for a low end card.
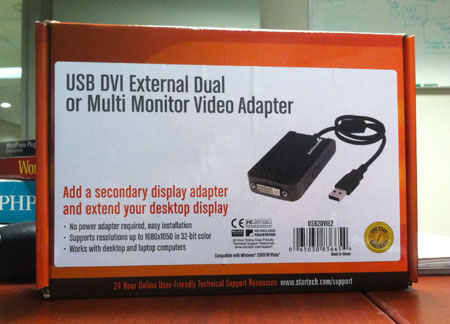
The goal was to just prop up another old 19 inch flat panel in addition to two other existing monitors. The box was an older dell that had a 1st generation PCIE card in it, and getting a cost- effective card to support eyefinity was out of the question. The goal was not to have 3D gaming on the display, rather to show financial and stock data. Because of the low cost, a Startech USB2DVIE2 adapter was purchased. Supporting a DVI monitor over USB, this cheap adapter allows adding up to 4 additional screens to a PC.
With 16MB of on board RAM, the adapter is listed as supporting up to a 1680×1050 resolution. Continue reading “Startech USB2DVIE2 USB display adapter”
Hanson Brothers BudIce Poster
From Mr. Ed’s brewerania collection:

Replacing batteries inside an Symmetra Battery Unit
The battery packs on an APC symmetra have a life span of around 5
years, and replacing all of them at once is an expensive proposition.
In an attempt to cut costs, I decided to replace the individual
batteries that make up each unit.
APCs SYBT4 part number refers to a 4 pack of the individual SYBTU1-PLP
part, which is a long chassis with a handle at one end and a connector
at the other. Each SYBTU1 contains eight individual batteries, and a
small circuit board.
 The batteries found in my particular unit were Vision CP1270s, 12V and
The batteries found in my particular unit were Vision CP1270s, 12V and
7.0 AH rated. You can get these batteries from online vendors such as
osi battery. They are available with the F1 or F2 designator that
indicates the size of the terminal on the battery – for the APC
project, we wanted the f2 batteries with the 1/4 inch lug.
So, once you have gotten your eight batteries, you can get started.
Pop the case by removing 8 screws, and slide back the cover.

Continue reading “Replacing batteries inside an Symmetra Battery Unit”
MySQL drops leading zeroes from imported US zip codes
After importing a table from a csv import, MySQL drops the leading zero from those codes that contain it. A quick way to fox this is to use a SQL query to update the table.
Log into the correct database in phpMyAdmin and open the table in question
Choose the SQL option from the tabs at the top
Paste the following query in to the box
UPDATE table_name SET ZipCode = concat(‘0’,ZipCode) WHERE length(ZipCode) = 4
Modify the statement to fit your situation, including table name and the zip code field name if needed. If you look at the code, you can tell that this will only work for a 5 digit code.
Execute statement and check the result.